GCST Technical Resources
Home / Resources
GCST Service
GCST services are delivered by the experts within our Professional Services Team. Contact us to learn more about how our methodology and how working with GCST Professional Services Organization can benefit your company.

White Papers
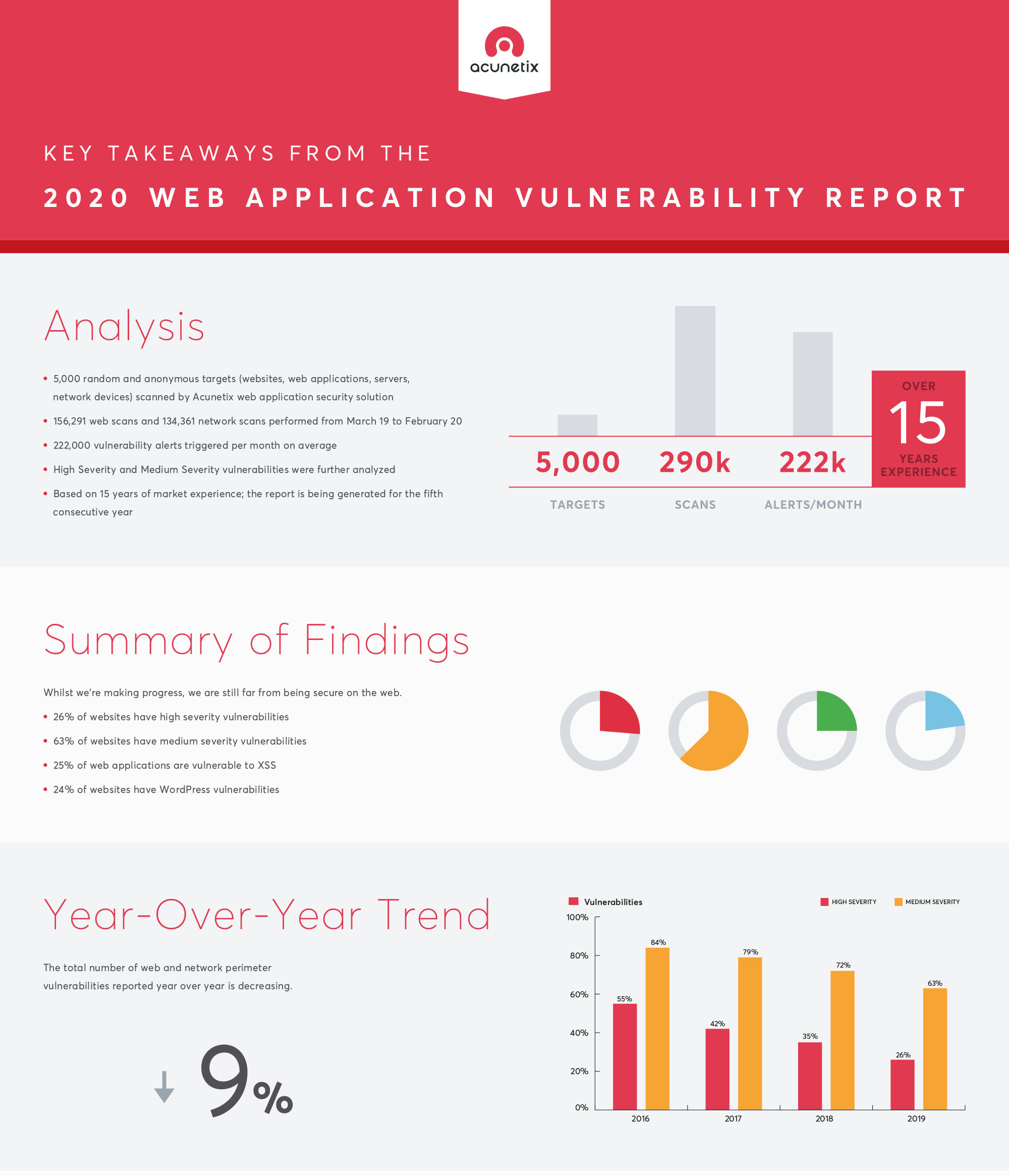
Acunetix Web Application Vulnerability Report 2020
Every year, Acunetix publishes an in-depth report of the most common web security vulnerabilities and network perimeter vulnerabilities. Download the report here.
Proactive Steps for Managing Cloud Costs
Growth in cloud use and spend is accelerating. Factor in the increased number of vendors offering services and applications via the cloud and it becomes even more imperative for businesses to understand, optimise and manage their cloud spend as much as possible. Download the report here.
Software License Optimization for Federal Agencies
Federal agencies spend billions of dollars a year on software. Unfortunately, a good portion of that spend is wasted because agencies underutilize their software licenses. This white paper discusses why waste occurs and the benefits of automated software optimization. Downlaod teh report here.
The Future Is the Web! How to Keep It Secure?
Web technologies are the core of the Internet. They are already adopted by email, communications, mobile applications, and more. They are making their way into innovative solutions such as the Internet of Things. To keep your enterprise secure, you need to build a strategy that includes securing the web. Download the report here.
Videos
Acunetix Deep-dive
This deep-dive covers how to quickly get started with scanning a website or web application for vulnerabilities, analyzing scan results and managing vulnerabilities with Acunetix.
Flexera Cloud Management Platform (CMP)
So I’ve migrated to the cloud, what’s next?
Learn how with Flexera’s cloud management platform you can manage a wide array of clouds and cloud services for AWS, Microsoft Azure, Google Cloud Platform, VMware vSphere, and more.
What’s New in Acunetix v13
Find out what’s new in Acunetix v13. The new release comes with an improved user interface and introduces innovations such as the SmartScan engine, malware detection functionality, comprehensive network scanning, proof-of-exploit, incremental scanning, and more. This release further strengthens the leading position of Acunetix on the web security market.
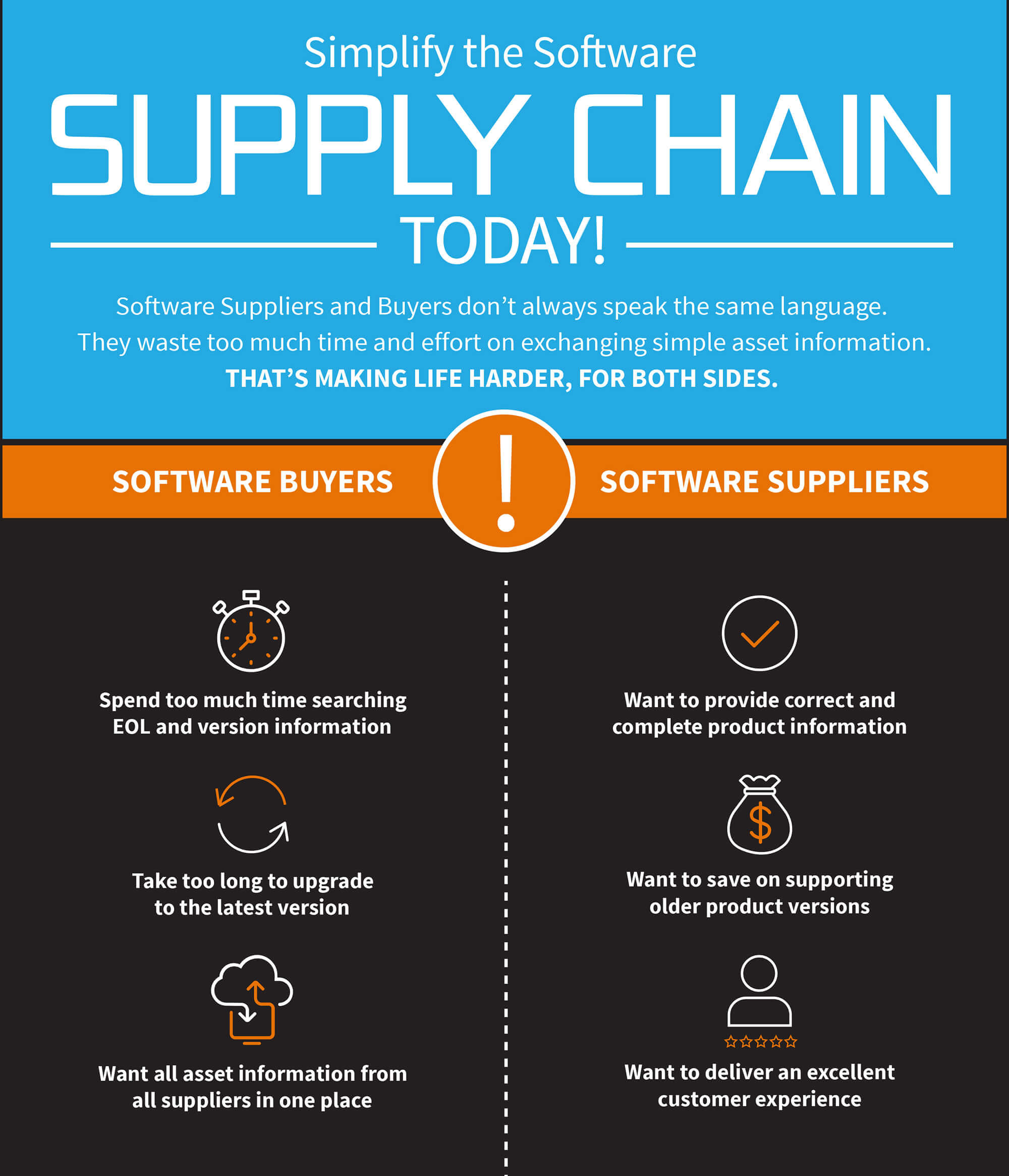
The Truth Is Flexera is Reimagining the Way Software is Bought, Sold, Managed, and Secured
Flexera helps organizations meet the challenges of a dysfunctional software supply chain where licensing is highly complex and software contains security vulnerabilities. Our software asset management, vulnerability management and composition analysis solutions allow IT Operations, IT Security, Development and Procurement teams to work together to reduce software and cloud services costs, maintain license compliance and mitigate security risks.
Infographics
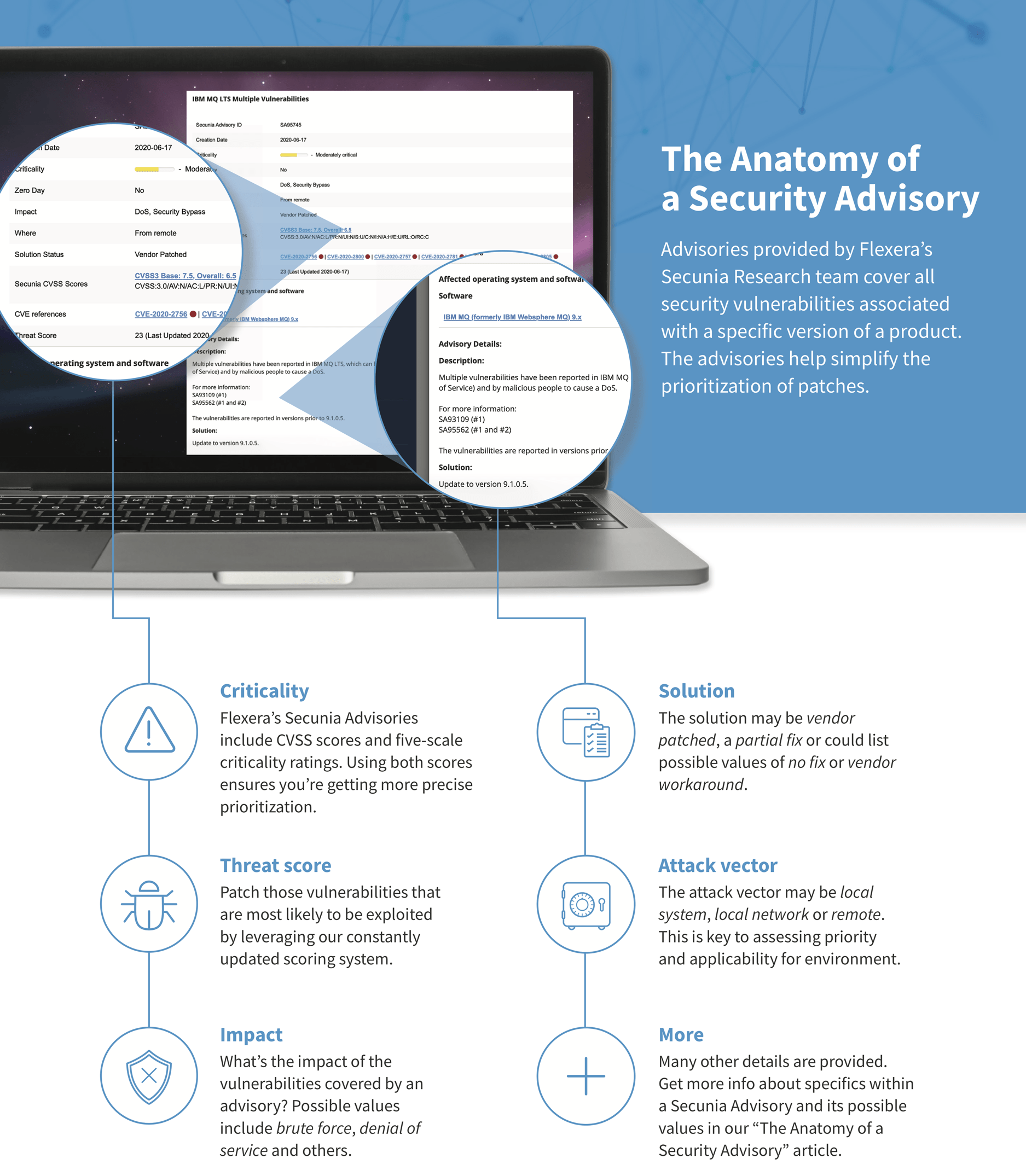
Anatomy of a security advisory
Since 2002, Flexera’s Secunia Research team has been delivering security advisories that provide reliable, curated, and actionable vulnerability intelligence. Applied within several Flexera solutions for different use cases, Secunia Research data enables you to focus on what truly matters by distilling vulnerability findings down to a single advisory perfect for prioritizing remediation efforts.
Anatomy of a security advisory
Since 2002, Flexera’s Secunia Research team has been delivering security advisories that provide reliable, curated, and actionable vulnerability intelligence. Applied within several Flexera solutions for different use cases, Secunia Research data enables you to focus on what truly matters by distilling vulnerability findings down to a single advisory perfect for prioritizing remediation efforts.
Key Takeaways from the 2020 Web Application Vulnerability Report
If you don’t have time to read the whole 2020 Acunetix Web Application Vulnerability Report, we have prepared two comfortable options for you. We want to make sure that you know the current state of web security so that you know what efforts to focus on in the future.
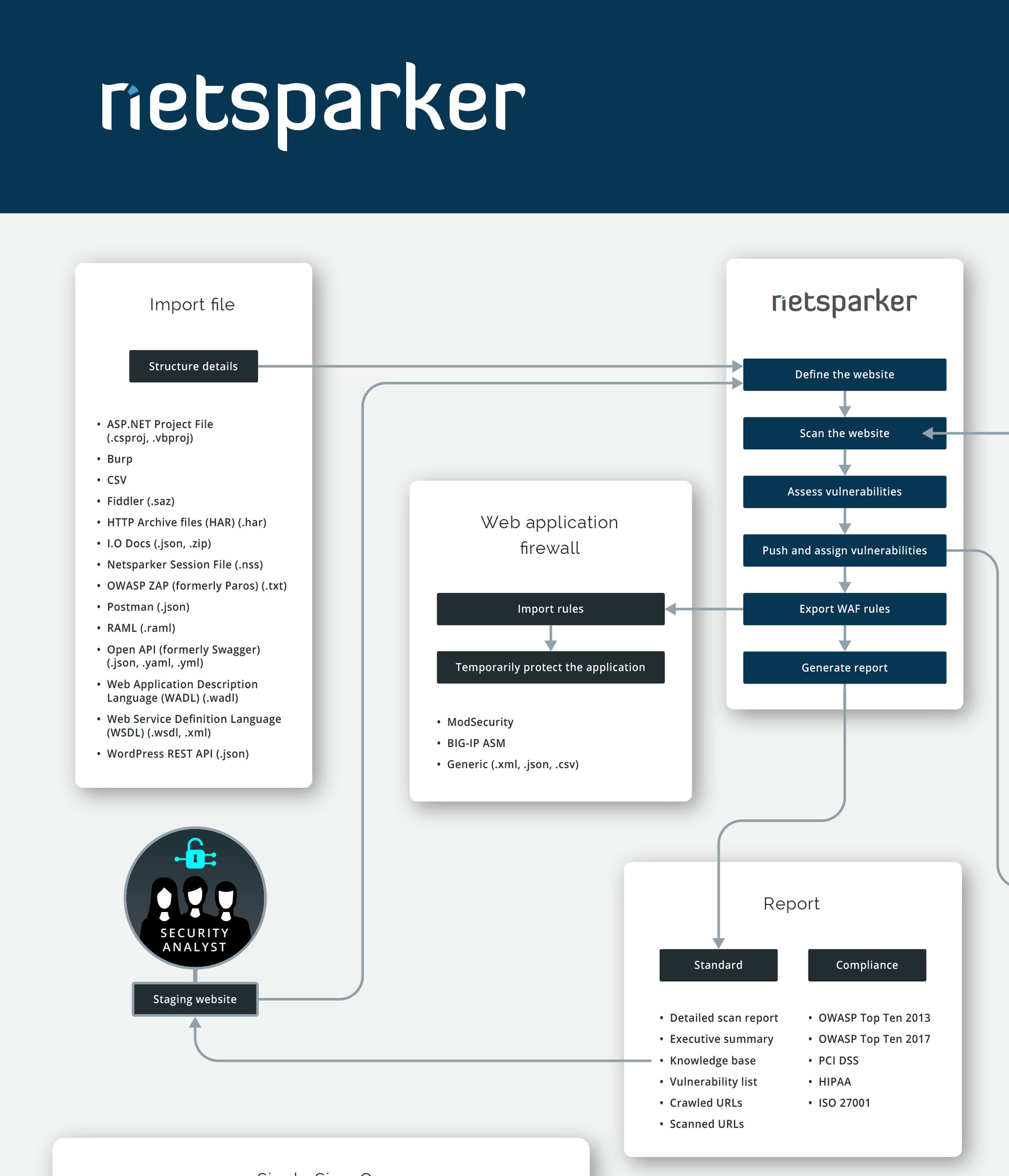
How Netsparker Works
Netsparker is a complete web application security solution that integrates with your issue trackers, vulnerability management systems, and CI/CD platforms. This allows you to fully incorporate web app security into your Software Development Life Cycle (SDLC).
View this info-graphic to see how Netsparker works and what tools it integrates with at a glance.
Tools
Acunetix Free Manual Pen Testing Tools
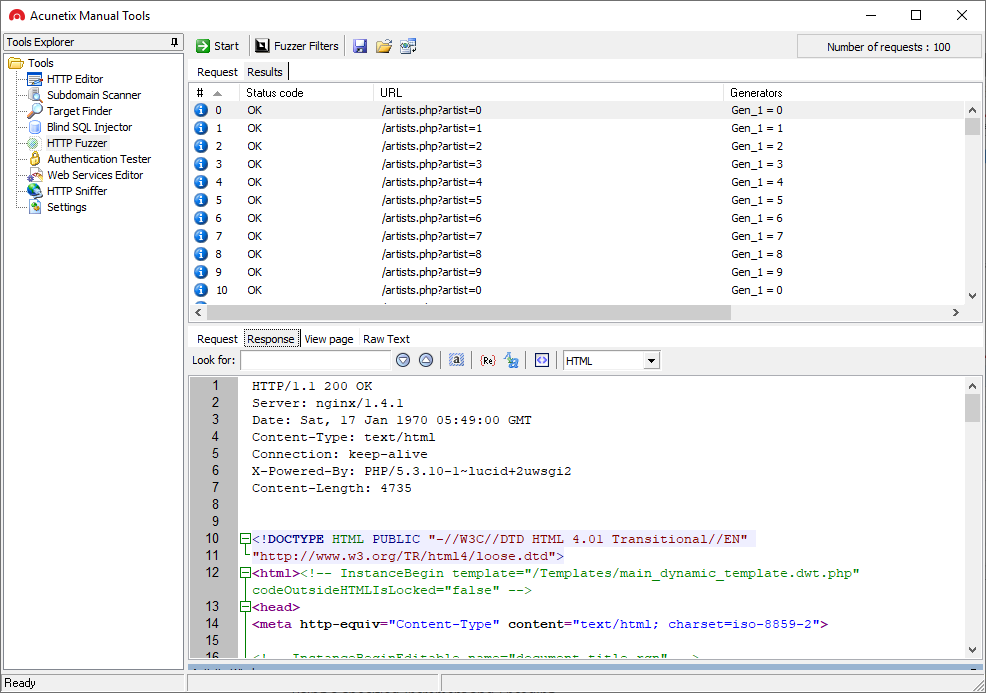
Acunetix Manual Tools is a free suite of penetration testing tools. These tools are not part of the Acunetix product and you need to download an installation package separately. Acunetix Manual Tools include 8 modules: HTTP Editor, Subdomain Scanner, Target Finder, Blind SQL Injector, HTTP Fuzzer, Authentication Tester, Web Services Editor, and HTTP Sniffer. Acunetix Manual Tools are free for private and commercial use but they are not an open-source project. Currently, they are only available for the Microsoft Windows operating system. The tools use a graphical interface only and do not support the command line. Penetration testers can use Acunetix Manual Tools with other tools such as the Metasploit exploitation framework, OWASP Zed Attack Proxy (ZAP), w3af audit framework, Wireshark, etc. to expand their knowledge about a particular security issue detected by an automated web vulnerability scanner or to find advanced security vulnerabilities that automated scanners cannot detect. A combination of automatic and manual tools is the best solution for a web application security testing framework. Automated scanners save a lot of time while manual tools let pen testers explore deeper.