Trusted by Dubai Government and proud member of Federal and Dubai SME
IT Management & Cyber Security
Our team provide a complete range of IT and OT solutions to variety of government and private sectors across Middle East Region. To deliver a successful integration of complex systems requires both specialized skills and the right level of experience. Our team consists of highly certified professionals with many years of experience in the IT & Cybersecurity industry.
Business Management Solutions
We provide business process management solutions to meet your company’s needs. Be it accounting, customer management, sales pipelines, or manufacturing processes, we have got you covered with our great products and superior consulting services. Smart ERP solutions for Small to Midsize Businesses are at the core of all that we do at GCS Management Solutions!
Marketing Solutions & Services
We build effective approaches to help you reach customers and prospects across the entire web. We are your extension of your marketing team and works towards making sure you achieve your objectives. by offering services like Brand Management, Social Media Management, Strategic planing and many more..

Why Choose Us
We are not product driven company, we focus on solutions customized and required for corporates by having:
- SME Approved Company
- Helping your Business from A to Z.
- Cyber Security Solution Experts
- Government and Enterprise Level Services
- Multilingual consultants
- vast knowledge around IT & Business Management.
- Successful Enterprise level ITSM & SAM Projects
- Certified Technical Experts.
- Local support.
- best of breed technologies!
Our Service
We believe every organization has unique requirements and expectations, thats why we start our job by consulting, education and services, solution selling is last step when we are sure what are the customer requirements and what suites the enterprises.
Local and International Software Asset Management & Cybersecurity Consultant in the UAE & Middle East.
Consulting
- IT & Business Management
- Cyber Security
- Software & Hardware Asset Management
- Selecting Right Solution
- Helping identifying Training requirements
- Project Management
- Marketing & Go-to-Market Strategy
Professional Services
- Design and Implementation
- Commissioning
- Monitoring & Management Services
- Health check
- Streamline workflows
- ensure data secuirty compliance
- Complete CyberSecurity Design
- Managmenet Consulting services.
Academy
- SAM Academy
- Security Awareness
- Advanced Cyber Security
- Artificial Intelligence
- Internet of Things
- Secure Coding
- Machine Learning
- ERP, CRM, Mareting tools
Behind the Story
We are enterpise focus and customize our services based on every projects and this is the reason of our sucess!
Projects Done
Consultants
Technology Partners
Happy Customers
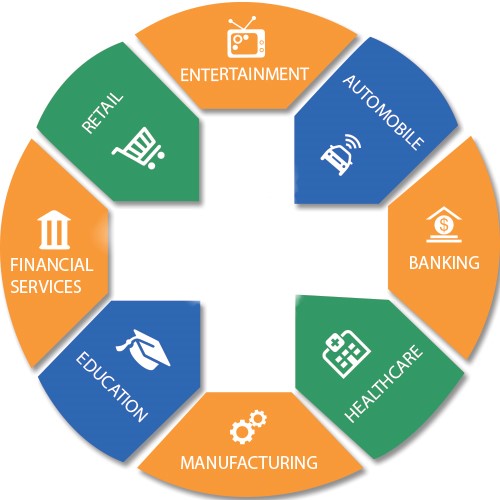
Our Customers
-
Bank & Financial Institution
-
Oil & Gas
-
Government
-
Enterprises
-
Industries
-
Educational Institution
-
Law Firms
-
Media
- Private, Retail and Insurance
Latest News

Monolithic vs microservices architecture: Which is better for security?
Monolithic vs microservices architecture: Which is better for security?

From home to any destination: How remote connectivity enhances work productivity
From home to any destination: How remote connectivity enhances work productivity

Private browsers: a beginner’s guide
Private browsers: a beginner’s guide
Why You need us?
Ready to get started?
Get in touch, and book your FREE consultancy.